The following is an article by Ari Buchler, a board member, operating partner, advisor, and angel investor to several software companies and private equity firms. He has held numerous business and legal executive roles, including Chief Legal Officer at Intralinks and General Counsel at Sophos. He has served as an advisor to LinkSquares since 2016.
The following is an article by Ari Buchler, a board member, operating partner, advisor, and angel investor to several software companies and private equity firms. He has held numerous business and legal executive roles, including Chief Legal Officer at Intralinks and General Counsel at Sophos. He has served as an advisor to LinkSquares since 2016.
In the wake of some recent cyberattacks in the past year, security professionals are recommending a new tactic to enhance protection from hackers: intelligent and proactive contract management. This may not have seemed an obvious path to many security professionals and executives but, the truth is, this is merely the extension of an old security tactic to modern times. And it’s overdue.
Not only is intelligent and proactive contract management a necessary area of cybersecurity focus, it’s never been easier to use modern software to automate much of your contract management to help augment your security posture.
So, why the heightened concern about contract management in security circles? Three words: Supply chain attacks.
A supply chain attack occurs when hackers attack an organization not through a direct assault on its systems, but rather through an assault on software or technologies supplied by third parties to the target organization. Using a supply chain attack, hackers can actually target many organizations at once by exploiting the security vulnerabilities of those organizations’ suppliers.
SolarWinds supplies a popular network monitoring software solution called Orion to 425 of the Fortune 500 companies as well as the US State Department and Department of Defense. Possibly as early as January 2019, SolarWinds got hacked by Russian state cyber-operatives, who used Orion to implant spyware on thousands of systems at hundreds of companies and government agencies.
In other words, Russia didn’t hack the State Department or other Solarwind clients directly; it hacked one element of their software supply chains. Russia was effectively reading state and industry secrets thanks to their compromising of SolarWinds, who unwittingly passed that vulnerability on to their customers via system updates.
Another example of a recent supply chain attack involves Kaseya, whose endpoint management and network monitoring product, VSA, is used by an estimated 37,000 customers, including Managed Service Providers (MSPs), who in turn serve thousands of their own customers. Over the recent July Fourth weekend, hackers leveraged a vulnerability in Kaseya‘s VSA software to infect dozens of Kaseya’s client systems with ransomware. However, since many of Kaseya’s clients include MSPs, this attack impacted an estimated 800-1,500 organizations, many of them small to medium size businesses.
So, what does all of this have to do with intelligent and proactive contract management?
Parties’ obligations to each other are normally set forth in written contracts. The more complicated the products and services, the more detailed the contract. This is especially true of contractual provisions related to cybersecurity, which have seen a significant increase in complexity over recent years.
Contractual obligations around cybersecurity will usually be a mix of technical and procedural requirements, and may specify adherence to industry-recognized cybersecurity frameworks. (In the case of U.S. government contracts, many of these issues are covered in Federal Acquisition Regulations that are incorporated by reference into contracts.) Contracts will also detail the process that the parties must follow in the event of a data breach, as well as any other remedies that are available to each party.
This is where contract management comes into play.
The best time to deal with these issues is of course during contract negotiations, where your leverage relative to the other party will significantly impact the extent of your success in negotiating favorable provisions. The reality is, however, that you likely have anywhere from dozens to hundreds -- even thousands -- of contracts that have been signed over a period of years. In many (if not most) cases, the contractual provisions around cybersecurity will be very outdated and will not reflect the current threat environment, currently available protective technologies, or the evolving regulatory requirements in this area.
Recognizing the limitations of relying on possibly outdated contract provisions in the wake of the Kaseya attack, the U.S. Cybersecurity & Infrastructure Security Agency (CISA) published an advisory that specifically recommended that all businesses:
“Review contractual relationships with all service providers. Ensure contracts include: Security controls the customer deems appropriate by the client; Appropriate monitoring and logging of provider-managed customer systems; Appropriate monitoring of the service provider’s presence, activities, and connections to the customer network; and Notification of confirmed or suspected security events and incidents occurring on the provider’s infrastructure and administrative networks.” [Emphasis mine.]
According to CISA, every security professional should be in the contract management business going forward. For security pros in regulated industries, this will be familiar.
In the US, HIPAA has for years required healthcare providers to sign Business Associate Agreements (BAAs) with any supplier or partner that could access confidential patient medical information, thereby extending HIPAA’s obligations to those suppliers and partners.
Internationally, the Payment Card Industry (PCI) has for decades required that any person, company, or software system with access to credit card numbers and transaction data commit to PCI security standards in writing.
CISA is now recommending that every business in every industry review the contracts of all their suppliers to make sure those suppliers are keeping your data secure. (Although the CISA advisory addresses supplier contracts, keep in mind that you may be both a customer and a supplier in a supply chain, in which case you want to make sure that you don’t end up with commitments to your client that exceed your suppliers’ commitments to you when it comes to cybersecurity.) Fortunately, this advice comes at a time when intelligent contract management tools are more advanced and more affordable than ever before.
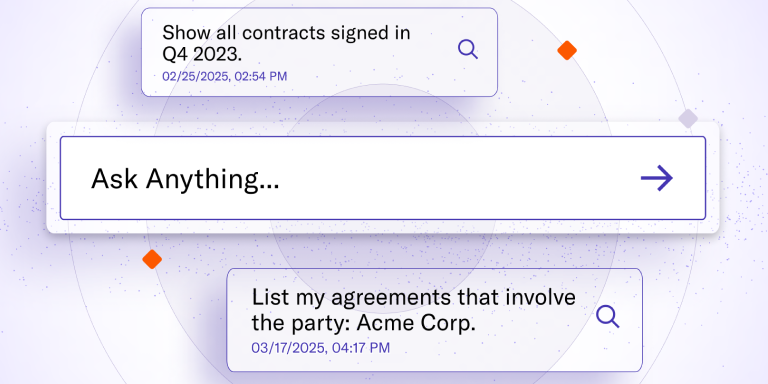
Modern contract lifecycle management (CLM) software uses artificial intelligence to parse and analyze contracts, so you can run a quick report on all your legal agreements -- supplier contracts included -- to see which ones include cybersecurity language, and what specific security practices are guaranteed in writing. These newer system capabilities go well beyond extracting mere data from contracts (e.g., parties, dates, fees), and allow the user to gain a fuller understanding of each parties’ obligations and to assess where gaps may exist.
In fact, CLM software is so fast and easy to use these days, you can extend your security review further down the supply chain. After all, you didn’t have to be a customer of SolarWinds or Kaseya to be affected by those attacks. You just had to be a customer of one of their compromised customers.
As CISA recognizes, proactive and intelligent contract management must now be part of security best practices. Supply chain security demands it. A good contract management solution should be added to your cybersecurity arsenal as soon as possible.
Download the eBook “How to Use LinkSquares to Improve Your Cybersecurity” to learn how you can use LinkSquares to improve your contract management and your cybersecurity posture.
Subscribe to the LinkSquares Blog
Stay up to date on best practices for GCs and legal teams, current events, legal tech, and more.