Welcome back! This post is part two in a series teaching you how to prevent and survive a data breach. If you missed part 1 about listening to experts and being proactive, check it out here. In this post, we’ll get into the third and final step in the process: how to write contracts that set you up for success. Let’s dive in.
Step 3: Write Smarter Contracts
The possibility of a data breach is inevitable; all that is unknown is the timing, the scale, and your level of risk. You can mitigate that risk by writing contracts with data breaches in mind. Working with technology, you can efficiently update your legal agreements to address each of the following clauses in the context of possible future data breaches:
Governing Law
National standards like the EU's General Data Protection Regulation (GDPR) may dictate the privacy expectations of your customers and partners, but you are still well-advised to stipulate the governing law for adjudicating any compensation for violating such a standard, as well as the jurisdiction that will rule on your contractual obligations in the event of a breach. Don't assume that national law covers all the bases here. Venue matters.
Data Access: During and Post-Severance
The "data conduct" of your partners and service providers can drive your own liability, so you need to explicitly spell out who has access to what during the term of your relationship and what materials must be returned, purged, or maintained once that relationship is severed. Clarity here benefits everyone. It prevents data from "lying around" after it is no longer of use, but is still at risk.
Reasonable Notification Periods In Event of Breach
Customers and partners will likely insist on some form of compensation in the event of a data breach if only to establish that your company has an incentive to protect their information. That said, clearly setting out compensation standards and maximums in advance can limit the direct and indirect costs of an eventual breach. Don't leave these numbers to chance or negotiation after the fact.
Limit Grounds for Termination or Compensation
As we’ve said, data breaches are somewhat inevitable. So, the mere fact of a breach should not be reasonable grounds for offering (or even receiving) compensation from or the termination of a legal agreement. Establish a minimum scope or type of breach -- for example, the disclosure of uniquely identifying information such as credit card or social security numbers -- as grounds for liability. Hackers simply breaching your firewall and crashing your marketing website should not invoke payouts to all your customers.
Handling a Data Breach Requires the Full C-Suite (and the Right Software)
Most of the work to handle a data breach should occur before the breach happens, and much of the work done should be handled by the entire C-suite, not just the CIO. It involves the right people following the right procedures using the right software -- including Contract Lifecycle Management software (CLM).
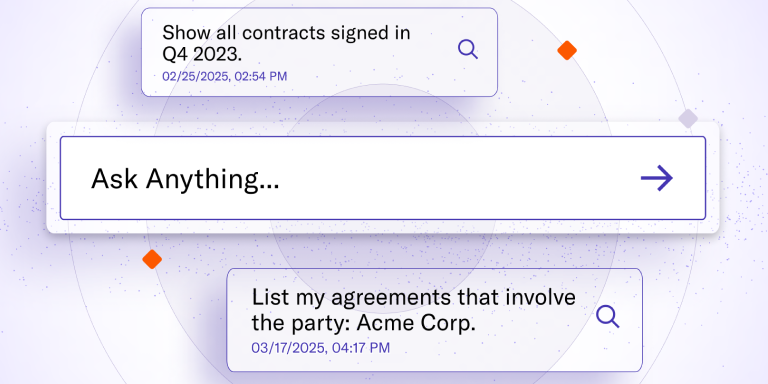
While security software can prevent and track the technical scope of a data breach, CLM can assess and minimize the contractual scope of a cyberattack. The proactive priority lists you should provide to your IT, customer service, and finance teams are easier to generate and update if you have a CLM solution that can identify the relevant legal agreements and their applicable clauses in real-time.
The updated contracts you need to minimize your liability if the face of future breaches are easier to create, update, and execute if you have a CLM solution that can show you where your current contracts are deficient, and track which agreements should be revisited.
If you're ready to get proactive about handling data breaches -- and include contractual impact in your cyber security regime -- contact LinkSquares today.

Subscribe to the LinkSquares Blog
Stay up to date on best practices for GCs and legal teams, current events, legal tech, and more.